14. Scenario: A Citrix Architect and a team of Workspacelab members have met for a design discussion about the NetScaler Design Project.
They captured the following requirements:
✑ Two pairs of NetScaler MPX appliances will be deployed in the DMZ network and the internal network.
✑ High availability will be accessible between the pair of NetScaler MPX appliances in the DMZ network.
✑ Multi-factor authentication must be configured for the NetScaler Gateway virtual server.
✑ The NetScaler Gateway virtual server is integrated with XenApp/XenDesktop environment.
✑ Load balancing must be deployed for the users from the workspacelab.com and vendorlab.com domains.
✑ The logon page must show the workspacelab logo.
✑ Certificate verification must be performed to identify and extract the username.
✑ The client certificate must have UserPrincipalName as a subject.
✑ All the managed workstations for the workspace users must have a client identifications certificate installed on it.
✑ The workspacelab users connecting from a managed workstation with a client certificate on it should be authenticated using LDAP.
✑ The workspacelab users connecting from a workstation without a client certificate should be authenticated using LDAP and RADIUS.
✑ The vendorlab users should be authenticated using Active Directory Federation Service.
✑ The user credentials must NOT be shared between workspacelab and vendorlab.
✑ Single Sign-on must be performed between StoreFront and NetScaler Gateway.
✑ A domain drop down list must be provided if the user connects to the NetScaler
Gateway virtual server externally.
✑ The domain of the user connecting externally must be identified using the domain selected from the domain drop down list.
On performing the deployment, the architect observes that users are always prompted with two-factor authentication when trying to assess externally from an unmanaged workstation.
Click the exhibit button to view the configuration.
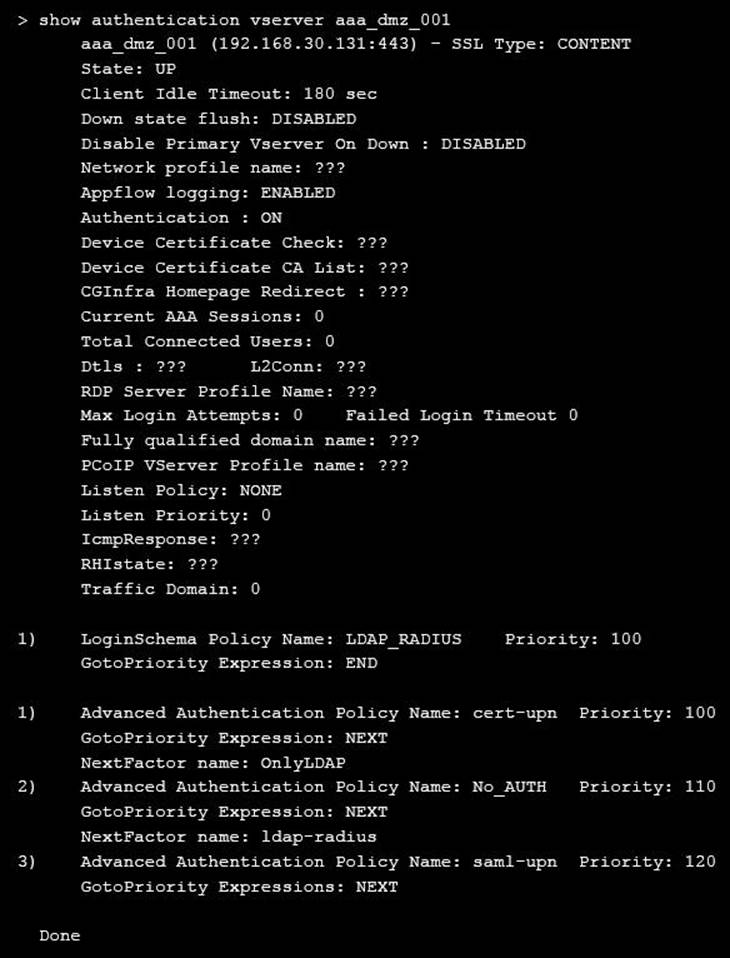
What should the architect do to correct this configuration?
